Two Israeli students from the Technion – Israel Institute of Technology discovered a massive vulnerability in the security of Microsoft’s virtual assistant Cortana, which allows users to operate their computer, smartphone, or smartwatch using voice commands. The threat enables even those who are not technologically savvy to breach a computer security and obtain complete access to a locked computer, with the ability to use the voice command system to install malicious software if they choose to do so.
The two third-year computer science students, Yuval Ron and Ron Marcovich, identified the potential threat with the use of voice interface to bypass security features, the university announced in mid-June. This is the first time that voice interface was used to dodge these security features in such a dangerous way, according to a university statement.
The students were able to download an external file, which allowed them to control all of the computer’s operations. The vulnerability allows for an instant security breach without any actual damage, the statement explained.
https://www.facebook.com/TechnionLive/videos/1871401466257284/
The students immediately reported their findings to Microsoft, who rewarded them through their Bounty Program, which offers payments of up to $250,000 to individuals who notify them of potential security issues. Microsoft issued a patch to protect against this form of attack in the future.
The students will also travel to Las Vegas to present their discovery at the Black Hat USA 2018 cybersecurity conference in August.
Ron and Marcovich further explained the vulnerability, which they dubbed the Voice of Esau (VoE,) on the Black Hat website, saying it “allowed attackers to take over a locked Windows 10 machine by combining voice commands and network fiddling.” The attacker can do this by pressing keys on the keyboard, while Cortana is voice activated from the lock screen.
In their upcoming presentation, Ron and Marcovich will also reveal a new vulnerability which they describe as more powerful and allows attackers to take over a locked Windows machine and execute arbitrary code.
“Exploiting this ‘Open Sesame’ vulnerability, attackers can view the contents of sensitive files (text and media), browse arbitrary web sites, download and execute arbitrary code from the Internet, and under some circumstances gain elevated privileges,” they wrote. Exploiting the vulnerability does not involve any external code or dubious system calls, making it potentially more harmful. Code-focused defenses such as anti-virus, anti-malware, and IPS would be blind to the attack, they said.
The students suggest “some defense mechanisms and compensating controls to detect and defend against such attacks.”
SEE ALSO: Spy Games: Ex-Mossad Chief’s Cybersecurity Startup Counters Attacks With A Hacker’s Mindset
Ron and Marcovich discovered the issues with Cortana as part of a Technion undergraduate course called Information Security Project, taught by Amichai Shulman, the founder of cybersecurity firm Imperva, Tal Be’ery, a security expert, and Professor Eli Biham of the Technion’s Hiroshi Fujiwara Cybersecurity Research Center. Shulman has served as an external lecturer for the course while contributing to the field of data security in the private sector. He also completed his undergraduate and Master’s Degree in the Technion Computer Science department.
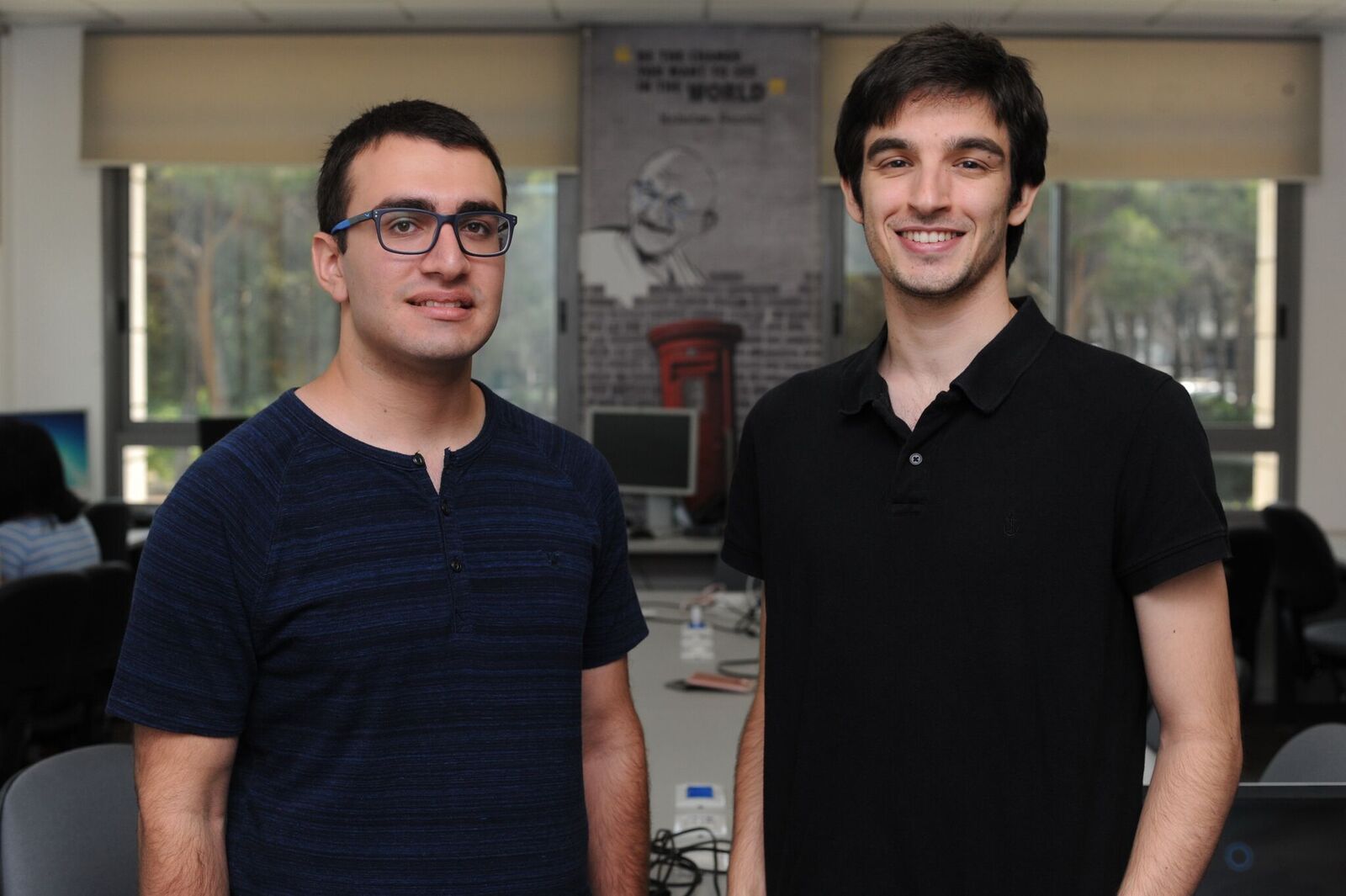
Ron Marcovich and Yuval Ron found a security breach in Microsoft’s voice-activated virtual assistant Cortana. Courtesy
Shulman has said this is the second time a security breach has been discovered through this student project. The first one, which also allowed for control of a voice command-locked computer, was presented at the Kaspersky Security Analyst Summit in March 2018.
Sign up for our free weekly newsletter
Subscribe“This recent breach is even more dramatic,” Shulman told the American Technion Society, “And I predict that this coming semester more teams will present significant findings regarding the dangers of combining a voice-command system with classical computer systems.”
Cortana’s development in Israel
This is not the first time an Israeli team has had a significant impact on developments at Microsoft.
Microsoft’s R&D activity in Israel, which currently has 1,100 development employees in Haifa, Nazareth, and Herzliya (and is in the midst of clearing out four floors at a Tel Aviv WeWork location on Dubnov street) was said to be actively involved in the original creation of Cortana before it was officially unveiled at Microsoft’s Build Developer conference in April 2014.
In its early stages, Microsoft decided to set up a Cortana development team at the company’s research and development center in Herzliya, Israeli news website Ynet reported last year. At the same time, Eran Yariv, then heading Israel’s Microsoft Innovation Lab, was told to take 20 people and start building a project. The rest is history.
Today, Yariv is the head of R&D for Cortana in Israel. While Cortana’s core development remains in the US and there are now a number of teams around the world, the Israeli team is one of the most prominent and involved in a variety of development aspects behind the scenes.
Yariv told Ynet that the team deals with big data, data processing, algorithm building, information analysis, and machine learning. They have also been involved in the development of new features for the voice assistant system, including one that allows users to ask the system to make calls.
Security Breaches
This isn’t the first time Israelis have had a hand in the discovery of a high-profile cybersecurity breach (and it certainly won’t be the last.)
SEE ALSO: Cybersecurity Nation: Why Israel Leads The World In Protecting The Web
Just last year, two major vulnerabilities were discovered. In December 2017, Israeli teen Yuval Sprintz found a breach in the Facebook-owned instant messaging and voice-over IP service app WhatsApp and reported it to the social network giant. A month earlier, US tech giants Google and Amazon released security updates for Google Home and Alexa devices after being warned by US-Israeli cybersecurity company Armis that the voice-commanded smart speakers were at risk for breaches from security threat BlueBorne.
Related posts

Editors’ & Readers’ Choice: 10 Favorite NoCamels Articles

Forward Facing: What Does The Future Hold For Israeli High-Tech?

Impact Innovation: Israeli Startups That Could Shape Our Future



Facebook comments