Popular off-the-shelf IoT devices including baby monitors, home security cameras, and thermostats are easily breachable, according to an ongoing study by Ben-Gurion University of the Negev cyber researchers, who said they hacked into most of the devices in about 30 minutes.
The study, according to a university statement, is part of ongoing research into detecting vulnerabilities of devices and networks now found as part of “smart homes,” businesses and in the medical field. In January, BGU researchers warned that unpatched medical devices, such as computed tomography (CT) and magnetic resonance imaging (MRI) machines are too exposed to cyber threats and easily exploited.
The current research looked into 16 popular IoT devices from high-end and low-end manufacturers, according to the researchers at the Implementation Security and Side-Channel Attacks Lab at Cyber@BGU, the university’s cybersecurity research center. The findings were published in a paper titled “Opening Pandora’s Box: Effective Techniques for Reverse Engineering IoT Devices.”
In it, the researchers detailed serious security and design flaws they uncovered in the common devices by disassembling and reverse engineering them. Using “fault injection-based techniques (introducing faults to test code paths) for bypassing password protection,” the researchers were able to “recover device firmware and passwords,” and “discover several common design flaws which lead to previously unknown vulnerabilities.

A web camera. Pixabay
Dr. Yossi Oren, a senior lecturer at BGU’s Department of Software and Information Systems Engineering and head of the Implementation Security and Side-Channel Attacks Lab at Cyber@BGU said, “It is truly frightening how easily a criminal, voyeur or pedophile can take over these devices.”
SEE ALSO: US-Israel Cybersecurity Firm Armis Warns Google, Amazon Of Airborne Cyber Attacks
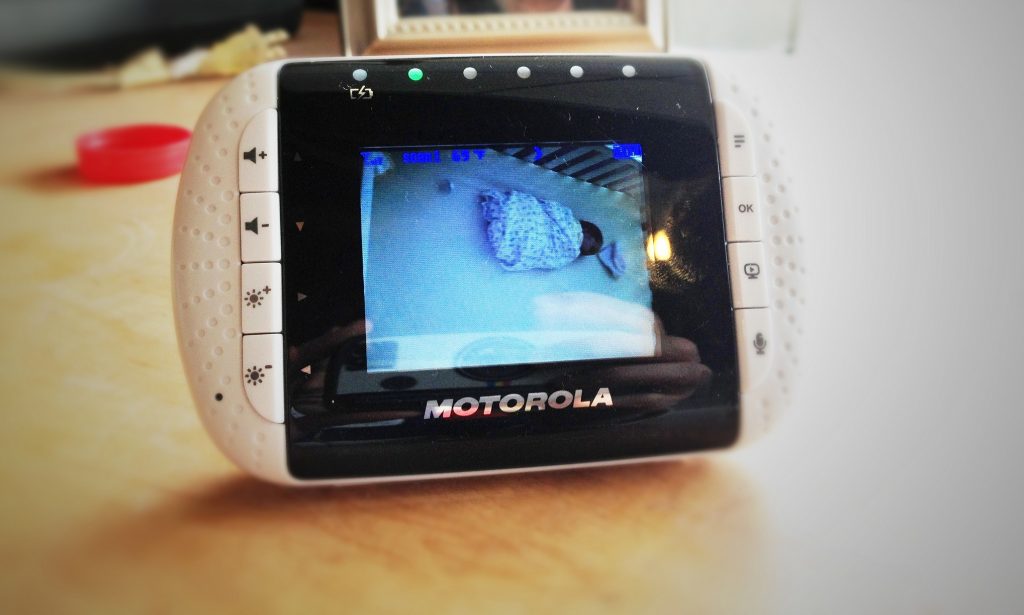
“Using these devices in our lab, we were able to play loud music through a baby monitor, turn off a thermostat and turn on a camera remotely, much to the concern of our researchers who themselves use these products,” he added.
Omer Shwartz, a Ph.D. student and a member of Dr. Oren’s lab said “it only took 30 minutes to find passwords for most of the devices and some of them were found merely through a Google search of the brand.”
Sign up for our free weekly newsletter
Subscribe“Once hackers can access an IoT device, like a camera, they can create an entire network of these camera models controlled remotely,” he warned.
Alarming stories of hackers breaching baby monitors have made numerous headlines in recent years, terrifying parents all over the world. In 2015, parents in Washington reported that their 3-year-old son told them he was scared of a voice coming from the monitor. The hacker was allegedly speaking to the child in the night and had said at one point, “Wake up little boy, daddy’s looking for you.” He was able to remotely control the camera and was also tracking the parents’ movements, they said. In another incident, a mother in Cincinnati woke up to a stranger screaming, “Wake up, baby! Wake up, baby!” into the monitor as her then 10-month-old was fast asleep. Some hackers have played strange music for babies and toddlers, and there are websites live-streaming footage from hacked baby monitors and home web cameras.

A baby sleeping. Pixabay
“The increase in IoT technology popularity holds many benefits, but this surge of new, innovative and cheap devices reveals complex security and privacy challenges,” said Yael Mathov, a Masters student who also conducted the research. “We hope our findings will hold manufacturers more accountable and help alert both manufacturers and consumers to the dangers inherent in the widespread use of unsecured IoT devices.”
Dr. Oren urged manufacturers to “stop using easy, hard-coded passwords, to disable remote access capabilities, and to make it harder to get information from shared ports, like an audio jack which was proven vulnerable in other studies by Cyber@BGU researchers.
“It seems getting IoT products to market at an attractive price is often more important than securing them properly,” he said.
SEE ALSO: How Israeli Cybersecurity Startups Are Battling The World’s Riskiest Online Hacks
The researchers issued a number of tips for ensuring security, including researching each device to “determine if it has a default password and if so change it before installing,” using strong passwords with a minimum of 16 characters, not using the same passwords for different devices, updating software regularly, and buying IoT devices only from reputable manufacturers and vendors.
Related posts

Editors’ & Readers’ Choice: 10 Favorite NoCamels Articles

Forward Facing: What Does The Future Hold For Israeli High-Tech?

Impact Innovation: Israeli Startups That Could Shape Our Future



Facebook comments