This article was first published on The Times of Israel and was re-posted with permission.
An Israeli company has put out a game that is not just for fun — it’s meant to prevent recurrence of the giant hack that a netted Russian gang 1.2 billion usernames and passwords in the “Heartbleed” fiasco. If it wasn’t obvious before, this backs up the insistence of Checkmarx that it’s time for attention to Internet security to move to the front seat.
If the UN’s statistics are correct, that 40% of the world’s 7.1 billion people use the Internet, then Russian hackers own one out of every three personal logins for social media sites, email, banking sites, and who knows what else, according to reports. How the Russian hackers got access to more than 1 billion usernames and passwords from hundreds of thousands of websites is a mystery — the company that unveiled the information, Hold Security, isn’t saying — but it could very well be connected to the enormous multi-year security foul-up that affected the Internet’s main security protocol, OpenSSL.
That security hole, which was apparently around for years before anyone noticed, is believed to have affected nearly one out of every five secure web servers — the ones that are supposed to be safe for submitting credit card information. According to some experts, Heartbleed is perhaps the biggest and worst security breach ever to hit the Internet. Why nobody noticed isn’t clear, according to Maty Siman, CTO and founder of Israeli security company Checkmarx, but it could be connected to the “back seat” security has often taken for programmers.
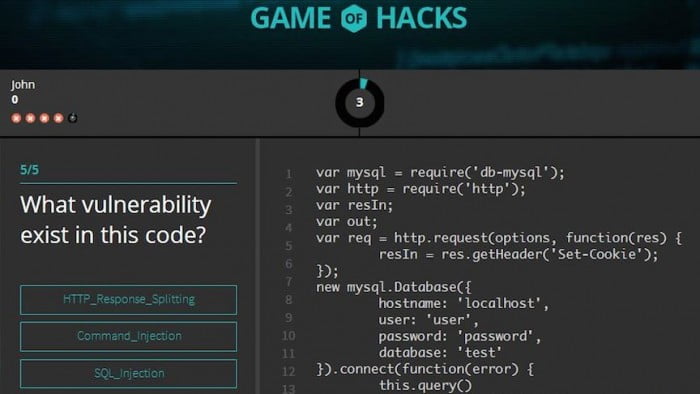
It’s a problem Checkmarx has been concerned with for some time now — and to improve programmers’ grasp of security issues, Checkmarx this week released the “Game of Hacks,” an online contest programmers can play against or computer — or each other — to help them identify the dumb mistakes programmers often make that opens the door to web thieves, who are able to easily penetrate site defenses and grab whatever data they want.
Heartbleed was the name given to a bug that was discovered in early April in the Internet’s Transport Layer Security (TLS) protocol, the open-source OpenSSL cryptography library. The bug, according to experts, may have been around for years.
To continue reading this article on the Times of Israel site, click here.
Photo by Marjan Krebelj
Related posts

Editors’ & Readers’ Choice: 10 Favorite NoCamels Articles

Forward Facing: What Does The Future Hold For Israeli High-Tech?

Impact Innovation: Israeli Startups That Could Shape Our Future




Facebook comments