Just a month and a half after the outbreak of the calamitous global ransomware “WannaCry,” a new worm that encrypts computer files and demands a ransom to decrypt them has wriggled its way into computers across the world.
Called “NotPetya” (after the similar Petya ransomware that wreaked havoc around the globe last year), the current attack started in Europe but is quickly spreading to the US and other countries.
Experts say NotPetya is among the most dangerous attacks the world has seen because targets include pharmaceutical companies, the Chernobyl radiation detection systems in the Ukraine, the Kiev transportation system, an airport and banks. One US hospital is also a victim of the latest hack.
SEE ALSO: Israeli Cyber-Security Experts Weigh In On WannaCry Ransomware, Offer Protection Tools
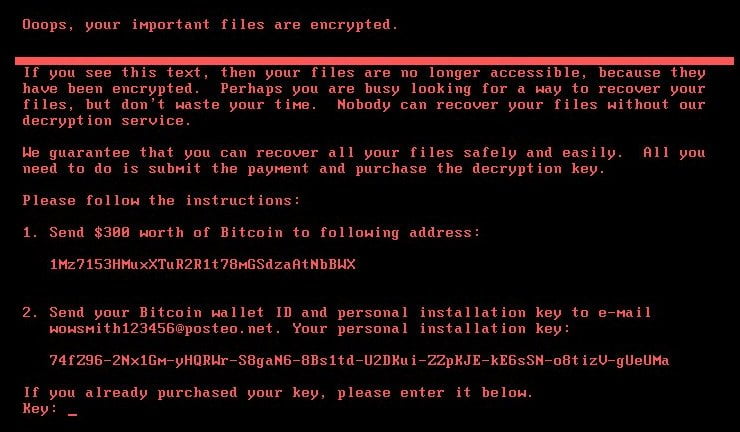
Computers infected by this massive attack get a black-and-red screen saying: “Oops, your important files are encrypted… Your files are no longer accessible. Perhaps you are busy looking for a way to recover your files, but don’t waste your time. Nobody can recover your files without our decryption services.” The message also contains instructions on how to wire a $300 ransom to the hackers.
Starting Tuesday, NotPetya has infected organizations across Europe, bringing business to a near standstill. Ukraine businesses have so far been the hardest hit. Supermarkets, gas stations and banks in the country, along with its public transportation system and major telecommunications providers report that their systems have been compromised.
Other affected organizations include British advertising agency WPP, Danish shipping company Maersk and Russian oil company Rosneft. The infection began Tuesday morning as European workers arrived at the office and turned on their computers and is believed to be spreading west.
According to Doron Sivan, CEO of Israeli cyber-security company Cronus Cyber Technologies, “the problem with this vulnerability is that it allows the malicious file to move within the network and continue to infect more and more computers. Since we live in a global village, the damage that was done in the Ukraine quickly affected customers and suppliers worldwide.”
SEE ALSO: Keeping The Lights On: Israeli Startups Protect Against Dire Cyber Attacks
According to Aviv Grafi, CTO of Israeli cyber-security company Votiro, last months’s WannaCry attack “was only the first among many ransomware campaigns. It seems that the ones in charge of the current attack have learned quite a lot from the WannaCry hackers.”
Sign up for our free weekly newsletter
SubscribeVotiro solutions apply an active cleansing process to all incoming files and email messages, neutralizing undisclosed exploits. The process is automatic and therefore does not rely on employees’ assessment of incoming files’ safety.
The Israeli who discovered the “kill switch”
Amit Serper, Principal Security Researcher at Israeli cybersecurity startup Cyebereason – which raised $100 million in the wake of WannaCry – says he has discovered a “vaccination” that disables the NotPetya ransomware. To activate the vaccination mechanisms users must locate the “C:\Windows\” folder and create a file named “perfc,” with no extension name. This should kill the application before it begins encrypting files.
SEE ALSO: Microsoft Buys Israeli Cybersecurity Firm Hexadite For Reported $100M
When first run, the NotPetya ransomware searches for its own filename in the “C:\windows\” folder, and if it is found, will cease operating. Once the original file name was found and verified by two different sources, Serper was able to piece together a “kill switch” that should work for any instances of the original ransomware infection.
Israelis are successful because they think like hackers
According to Jacob Benadiba, Israel’s Managing Director for business operations giant Accenture, only 17 percent of organizations invest in cyber-security solutions that would protect them, and cyber-attacks are successfully fought off in only one in three instances.
Further establishing what Israeli Prime Minister Benjamin Netanyahu said earlier this week about Israel’s leading position in cyber-security, Benadiba forecasts that “Israel will continue to lead the cyber-security market. International corporations like Accenture come to Israeli to seek cyber-security experts who think like hackers. When you approach cyber-security from a standpoint of a hacker, you know how to best protect your critical assets in a precise way.”
Photos and screenshots: Trend Micro, Accenture Israel, Pixabay
Related posts

Editors’ & Readers’ Choice: 10 Favorite NoCamels Articles

Forward Facing: What Does The Future Hold For Israeli High-Tech?

Impact Innovation: Israeli Startups That Could Shape Our Future






Facebook comments