The password needs to die, and SlickLogin is trying to help kill it.
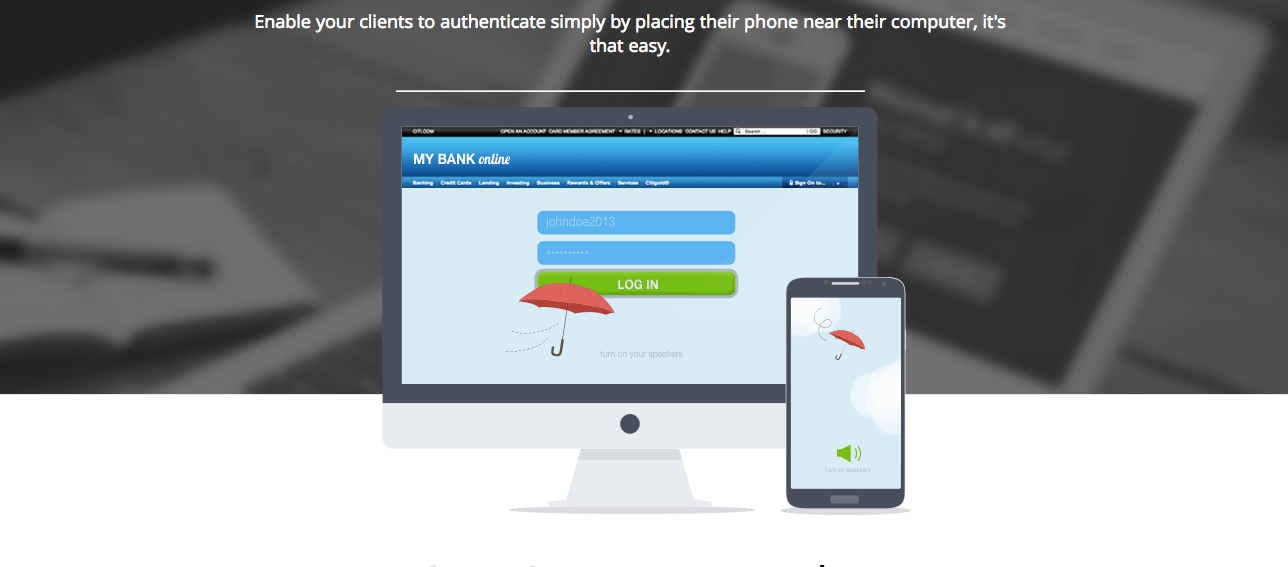
Launching into closed beta in the Disrupt SF 2013 Battlefield today, SlickLogin lets you log into a website on your computer by holding your phone within a few inches of it.
Here’s the idea: as a user, you’d go to whatever SlickLogin-enabled site you’d like to log in to. Tap the login button, hold your phone up close to the laptop, and you’re in. SlickLogin can be used either as a secondary verification layer to your existing credentials (think RSA keys or an SMS-based two factor system, without having to type any codes), or, if the service provider chooses, can forego username/password typing all together.
So, how does it work?
SlickLogin can use a bunch of protocols to start verifying your phone’s position: WiFi, Bluetooth, NFC, visual markers like QR codes, and of course, GPS. Their self-dubbed “secret sauce”, though, is their use of uniquely generated sounds intentionally made inaudible to the human ear. Your computer plays the sound through its speakers, while an app on your smartphone uses the device’s built-in microphone to pick up the audio.
Related articles
- Beyond Verbal Gets A $2.8M Seed Round To Develop Voice Recognition That Decodes Emotions
- VocalZoom’s Microphone ‘Reads Lips’ To Improve Sound Quality
Once it processes the sound and identifies that it’s you (or at least, someone with your phone) standing in front of your computer, it sends the green light up to the server to let you log in. SlickLogin doesn’t require your company to build a whole new mobile app; instead, you just add 5 lines of code to your existing app.
SlickLogin
This isn’t the first time we’ve seen high-frequency sound used to transfer data, of course. The as-yet unlaunched payments service Clinkle is said to use high frequency sounds to let users send money to others nearby. SonicNotify is using the concept to let TV advertisers and retail stores send content to handsets. Chirp is trying to build an entire file transfer protocol based on the idea. It is, however, the first time I’ve seen it used for logins and two-factor authentication.
…
To continue reading this article, click here
Via TechCrunch
Photo: Speech Recognition, Red Waveform by Bigstock
Related posts

Editors’ & Readers’ Choice: 10 Favorite NoCamels Articles

Forward Facing: What Does The Future Hold For Israeli High-Tech?

Impact Innovation: Israeli Startups That Could Shape Our Future



Facebook comments