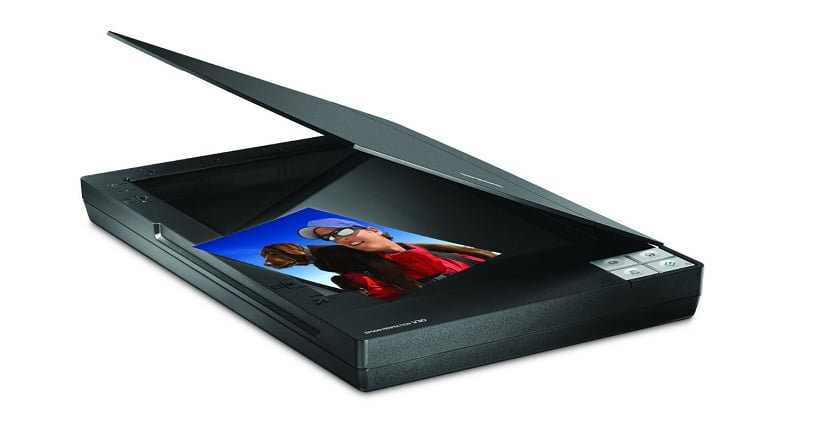
We’ve all heard about hackers remotely activating webcams and microphones to spy on people without their knowing. NoCamels recently reported that even simple headphones can spy on us. Now, new research reveals that a seemingly innocent desktop scanner can be hacked and manipulated to steal precious data from your computer.
According to a new study conducted by Israel’s Ben-Gurion University and Weizmann Institute researchers, a typical office scanner can be infiltrated and a company’s network compromised using different light sources. Moreover, desktop scanners can be hijacked to perpetrate cyber-attacks through drones hovering over your home or office.
SEE ALSO: Fan-tastic Hacking: Israeli Researchers Hack Into Computers By Listening To Their Fans
Don’t leave your scanner lid open
“In this research, we demonstrated how to use a laser or smart bulb to establish a covert channel between an outside attacker and malware installed on a networked computer,” BGU researcher Ben Nassi said in a statement. “A scanner with the lid left open is sensitive to changes in the surrounding light and might be used as a back door into a company’s network.”
The project was conceived by Weizmann Institute’s Prof. Adi Shamir in hopes to identify new network vulnerabilities by establishing a secret channel in a computer network. His team conducted several demonstrations to transmit a message into computers connected to a flatbed scanner. Using direct laser light sources up to a half-mile (900 meters) away, as well as on a drone outside their office building, the researchers successfully sent a message to trigger malware through the scanner.
Sign up for our free weekly newsletter
SubscribeSEE ALSO: How Israeli Cyber-Security Startups Are Battling The World’s Riskiest Online Hacks
In another demonstration, the researchers used a Samsung Galaxy 4 Smartphone to hijack a smart lightbulb (using radio signals) in the same room as the scanner. Using a program they wrote, they manipulated the smart bulb to emit pulsating light that delivered the triggering message in only seconds.
To mitigate this vulnerability, the researchers recommend organizations connect a scanner to the network through a proxy server – a computer that acts as an intermediary – which would prevent establishing a clandestine channel. However, this might be considered an extreme solution, since it also limits printing and faxing remotely on all-in-one devices.
But Nassi hopes his study, titled Oops!…I think I scanned a malware, “will increase the awareness to this threat, and result in secured protocols for scanning that will prevent an attacker from establishing such a secret channel through an external light source, smart bulb, smart TV, or other IoT (Internet of Things) devices.”
Ben Nassi’s Ph.D. research advisor is Prof. Yuval Elovici of BGU’s Department of Software and Information Systems Engineering, who’s also heading the Deutsche Telekom Innovation Laboratories at Ben-Gurion University.
Photos and video: Epson/Amazon, Ben-Gurion University
Related posts

AI Insurance Company Cuts Prices As Drivers Cut Phone Use





Facebook comments